- NordVPN Researchers uncovered a massive recruiting phishing scam.
- Scammers impersonate major global employers like Meta, Disney and Spotify
- Hackers use fake job boards to steal job seekers’ Facebook login credentials
The job market is tough enough without having to dodge cybercriminals. But according to new research from NordVPN, hackers are now posing as recruiters for some of the world’s biggest brands to hijack the social media accounts of unsuspecting job seekers.
The cybersecurity firm’s Threat Intelligence unit has exposed a highly sophisticated phishing campaign that weaponizes the names of major employers, including Meta, Disney, Coca-Cola and Spotify. Instead of stealing your money directly, the operation is designed to silently harvest your Facebook credentials.
By deploying slick recruiting emails, hidden “HUB” domains, and incredibly realistic job portals, attackers trick applicants into handing over the keys to their digital lives. Since social media accounts are often linked to other sensitive apps and services, a compromised Facebook login can quickly turn into a devastating privacy breach.
If you want to protect your personal data while applying for jobs online, using one of the best VPN services with built-in anti-malware and blocking malicious trackers is a smart first step. However, staying completely safe from spear phishing requires a deeper understanding of how these multi-stage scams actually work.
From a false job offer to total account hijacking
The campaign starts with a professional-looking cold email, often sent through legitimate platforms like Google AppSheet to bypass standard spam filters.
These messages feature clean grammar and target victims whose contact details were likely scraped from platforms like LinkedIn or exposed in previous data breaches.
By clicking the link in the email, victims access a “HUB” domain (such as careers.meta-findyourjob[.]com).
Interestingly, NordVPN discovered that these sites have a clever evasion tactic built in. If a security scanner or analyst visits the URL directly, they will only see a blank, harmless web page. The malicious “Search for Job” button is only activated when the site is activated via a unique referral link embedded in the original phishing email.
Once the victim clicks, they arrive at an intermediate site that perfectly mimics a legitimate corporate job board. Researchers identified several fake portals, including connect.spotifycareerapply[.]com for Spotify and jobquest.wdcfuturesteps[.]com for Disney.
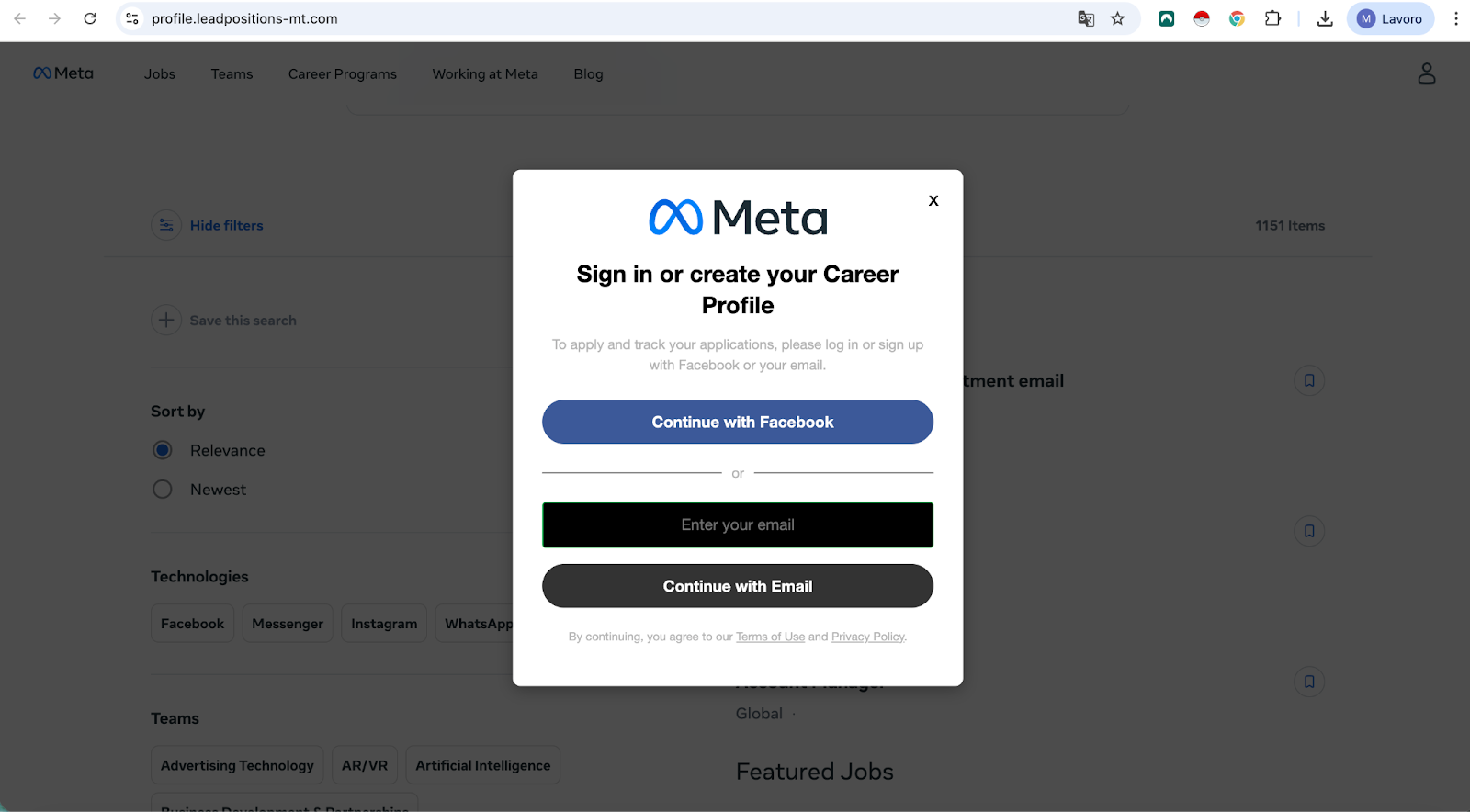
The trap is finally closed when the applicant clicks “Apply.” Instead of a standard application form, they receive a message requiring them to log in through Facebook to continue. This fake login page captures the victim’s username and password, giving attackers full control over the account.
Domininkas Virbickas, Product Manager at NordVPN, explains that job seekers are “exceptionally vulnerable” to these types of attacks. This is because they already have a mindset where sharing personal details and following instructions from unknown contacts is the normal process for getting an interview.
“These types of campaigns take advantage of that trust through sophisticated communications and convincing fake professional portals that are almost indistinguishable from the real thing,” Virbickas said.
How to stay safe during your job search
This campaign demonstrates that cybercriminals are constantly finding new ways to weaponize professional contexts to circumvent our natural skepticism. Because this stream of attacks so closely mimics a real corporate hiring process, even cautious Internet users can be caught off guard.
To protect yourself, NordVPN recommends getting into the habit of checking the URL before entering any personal data. Legitimate megabrands will always host their career pages on official, recognizable domains, not unusual third-party links.
The same rule applies to social login requests. An authentic “Sign in with Facebook” button will always safely redirect you to the official page. facebook.com domain. If the URL bar shows anything else, close the tab immediately.
If you still have doubts, I recommend running the link through NordVPN’s URL checker tool or similar software. It’s completely free for anyone, even those who don’t have an active NordVPN subscription.
Finally, NordVPN suggests always enabling two-factor authentication (2FA) on your social media profiles. Even if a sophisticated phishing page manages to steal your password, 2FA serves as a vital safety net that prevents attackers from accessing your account.
Follow TechRadar on Google News and add us as a preferred source to receive news, reviews and opinions from our experts in your feeds. Be sure to click the Follow button!




