- FTP still runs widely due to forgotten default settings
- Millions of servers expose FTP without active administrative knowledge
- Inconsistencies in encryption leave many FTP connections completely unprotected online
File Transfer Protocol (FTP) is one of the oldest methods of moving files over the Internet, designed during an era when online security was not a primary concern.
According to Censys, it still runs on nearly 6 million servers primarily because it was enabled by default within hosting panels and subsequently forgotten about, rather than maintained through a deliberate administrative choice.
Due to its persistent and often undetected operations, security experts are now questioning whether this 55-year-old protocol should be used at all.
Article continues below.
FTP continues to persist in modern infrastructure
“If FTP appears in your asset inventory, the first question is not how to protect it, but whether it should be running. Use a more secure alternative,” Censys warns.
A considerable part of the FTP exposure problem originates from control panel ecosystems that enable the protocol by default during initial server provisioning.
This means that the service often remains active through unattended configuration rather than through an affirmative choice made by the administrator.
Another major problem is that many FTP servers are deliberately not installed as a primary service.
They often come bundled with hosting platforms and control panels, where they are automatically enabled during setup.
Over time, they remain active without periodic review, making it difficult for organizations to know exactly how many FTP services they are running.
This creates silent risks that can go unnoticed for long periods within ordinary operations.
It also reflects a broader infrastructure pattern in which convenience-driven services continue to operate long after their original need has disappeared.
That persistence often leaves administrators unsure about what still matters, what can be eliminated, and what has simply been forgotten.
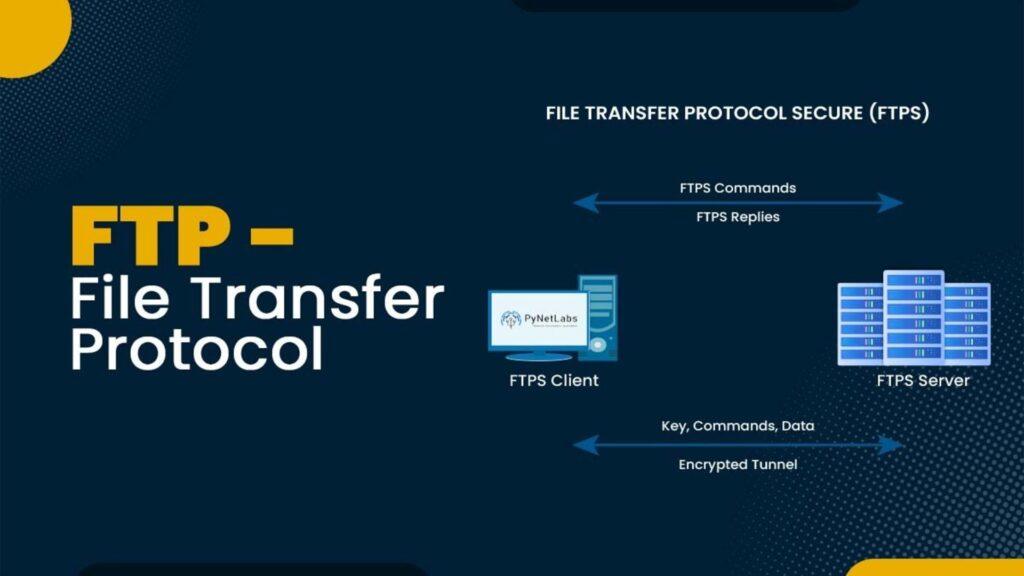
FTP’s handling of passwords and other sensitive data during transmission is a major concern.
In some configurations, FTP can still send login details in plain text, meaning they could be intercepted if someone is watching your network traffic.
Although some servers now support encryption, many still do not use it or are poorly configured for secure connections.
This inconsistency exists because support varies between software packages and is highly dependent on the installation choices made from the beginning.
As a result, organizations often face fragmented environments where some traffic is protected, while other connections remain exposed in clear text.
Security researchers also note that FTP daemons behave differently: some treat encryption as optional and others require administrative steps that are overlooked.
In practice, this results in inconsistent protection across the Internet, depending on how each server was originally configured.
Follow TechRadar on Google News and add us as a preferred source to receive news, reviews and opinions from our experts in your feeds.