- In 2024 a leaked directory containing US military data was found.
- Cybernews received a tip about the directory and launched an investigation
- Leaked directory remained accessible despite CISA being notified
A leaked directory containing more than 70,000 files related to military personnel records, contractor records and images taken inside military bases has been discovered.
Researchers of cyber news They were alerted to the leaked directory and investigated its contents.
Even though security researcher Arkadeep Roy reported it to the Cybersecurity and Infrastructure Security Agency (CISA) in 2024, the dataset remained exposed and was actively leaked in April 2026.
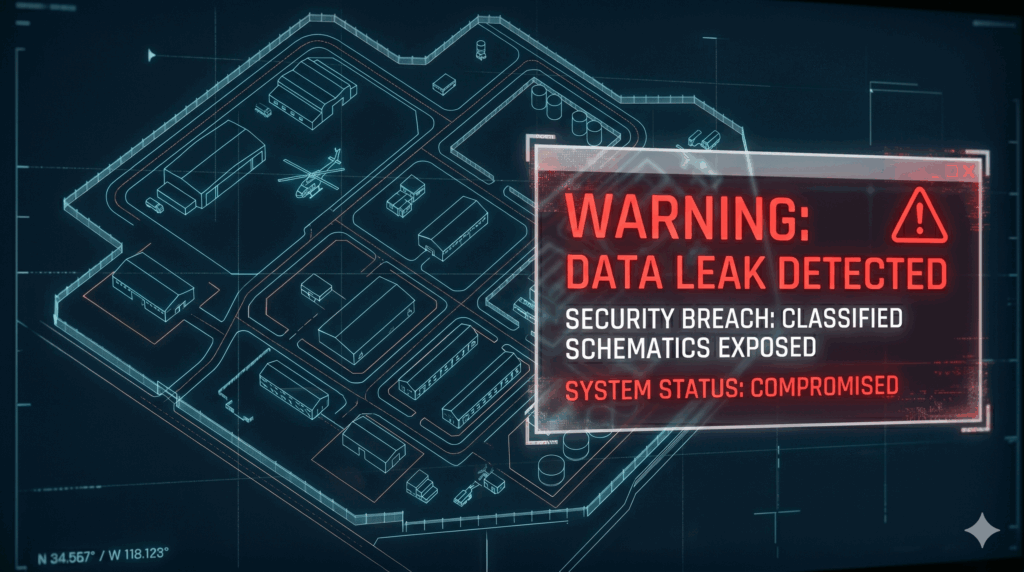
Schemes and personnel files exposed.
Cybernews discovered that the data set was exposed through an open directory listing vulnerability. The board also lacked sufficient security controls. The directory was found to belong to CMI Management Inc., a US government contractor, which is part of the Dexterra Group.
According to CMI Management’s website, the company specializes in providing government facilities services. The website states: “Over the years, CMI has successfully managed a wide range of government facilities, from training centers to mission-critical operations.”
The files were originally discovered in 2024 and CISA was notified the same year. On March 16, 2026, Cybernews received a tip about the exposed database and launched an investigation the next day. Cybernews confirmed the leaked directory and reported it to CMI Management and CISA on March 18, 2026.
Cybernews shared a series of example images that have been heavily redacted to censor private information. The images include maintenance forms, emails between staff and photographs of internal infrastructure. Cybernews alerted CMI Management about the leaked directory, but did not immediately receive a response.
The leak of sensitive information about personnel and contractors could put current and former US military personnel at risk of phishing or spoofing attempts, or personnel details could be used to gain unauthorized access to military facilities.
Of particular concern is the leak of internal photographs of US military bases and base schematics, which could be used by threat actors to create detailed maps of US military bases and identify weaknesses in both structure and security.
“The data breach is concerning, as sensitive US military data was stored insecurely for over a year, even after CISA was notified. This means that even when it comes to the military and its facilities, it is very common to find data stored insecurely, and remediation efforts are not prioritized even after notifying the relevant authorities,” the Cybernews investigative team said.
Following the Stryker Corporation cyberattack, CISA issued an alert in March 2026 with guidance on how organizations should harden endpoint management system configurations to defend against malicious cyber activity.
Follow TechRadar on Google News and add us as a preferred source to receive news, reviews and opinions from our experts in your feeds.